Secure IT Infrastructure 2087193265 Online

A secure IT infrastructure is critical for safeguarding sensitive information and maintaining operational integrity in today’s digital landscape. Organizations must evaluate their current security measures, focusing on risk assessment and compliance. Key strategies, such as network segmentation and advanced encryption, play a vital role. However, the human factor remains a significant vulnerability. Understanding how to effectively train employees can determine an organization’s overall security posture and resilience against potential threats. The implications of these strategies warrant further examination.
Understanding the Importance of a Secure IT Infrastructure
Securing an IT infrastructure stands as a critical priority for organizations in an increasingly digital landscape. Effective risk assessment is essential for identifying vulnerabilities and ensuring compliance regulations are met.
Organizations must prioritize security measures to protect sensitive data and maintain operational integrity. A robust IT framework not only mitigates threats but also fosters a culture of accountability and transparency, empowering stakeholders with the freedom to innovate safely.
Key Strategies for Strengthening Your IT Security
Implementing key strategies for strengthening IT security is essential for organizations aiming to safeguard their digital assets.
Effective network segmentation isolates critical systems, thereby minimizing attack surfaces.
Additionally, robust access control mechanisms ensure that only authorized personnel can access sensitive information.
Essential Tools and Technologies for IT Infrastructure Security
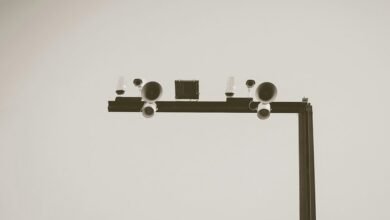
A robust IT security posture relies not only on strategic frameworks but also on the tools and technologies that facilitate their implementation.
Firewall configurations serve as the first line of defense against unauthorized access, while advanced encryption methods ensure data integrity and confidentiality.
Together, these essential components create a fortified IT infrastructure, empowering organizations to operate securely and maintain their freedom in a constantly evolving digital landscape.
Best Practices for Employee Training and Awareness in Cybersecurity
While technical defenses are crucial, the human element remains a significant vulnerability in cybersecurity.
Implementing robust employee training programs focused on cyber hygiene is essential. Regular phishing simulations enhance awareness, allowing employees to recognize and respond to threats effectively.
Conclusion
In a world increasingly reliant on digital operations, one might assume that a secure IT infrastructure is a given. Ironically, as organizations invest in advanced technologies and stringent access controls, they often overlook the human element—their employees. This paradox highlights that while sophisticated tools may shield against external threats, it is the untrained user who remains the weakest link. Thus, without a comprehensive approach that includes robust training, the very measures intended to protect could inadvertently expose vulnerabilities.